| Course Index |
|---|
| Part 1 – Introduction: What is IPv6 |
| Part 2 – IPv6 Addressing & Subnetting |
| Part 3 – IPv6 Headers & Header Extensions |
| Part 4 – ICMPv6 & IPv6 Neighborships |
| Part 5 – IPv6 Configuration, EUI-64, SLAAC & Dual Stack |
| Part 6 – IPv6 DHCP (DHCPv6) |
| Part 7 – IPv6 on Windows |
| Part 8 – IPv6 on Linux |
| Part 9 – IPv6 on Mac |
| Part 10 – IPv6 DNS, Monitoring & Address Management |
| Part 11 – IPv6 Routing |
| Part 12 – IPv6 Security & Tunneling |
| Part 13 – IPv6 Internet Connection & Address Planning |
IPv6 Foundation Part 5: IPv6 Configuration, EUI-64, SLAAC & Dual Stack
IPv6 Configuration on your Devices
Now that you know all important basics about IPv6, let’s have some fun and jump into configuration on some devices.
In the examples I use some common platforms such as Cisco IOS, HP ProCurve, HP/H3C Comware, Juniper JUNOS, Apple MacOS, Microsoft Windows and Linux.
Please feel free to do more research and testing using other platforms. There are some nice lab simulators on the internet that can be used to configure virtual or physical routers without the need to purchase and run them in your home (which I did back when I learned about networking). You can also emulate some routing gear on Cisco’s Virtual Internet Routing Lab (VIRL) and different operating systems using commercial and free virtualization software, such as VirtualBox.
I learn best by a lot of practice and playing around, maybe this works for you, too!
Types of IPv6 address assignment
How to configure Static IPv6 Addresses
I put together a static configuration comparison in the following table. As you can see, there is not much difference for the major networking vendors in regards to configuration syntax.
| Platform | IPv4 | IPv6 |
|---|---|---|
|
Cisco IOS |
interface vlan 23 |
interface vlan 23 |
|
HP/H3C Comware |
interface vlan 23 |
interface vlan 23 |
|
HP ProCurve |
interface vlan 23 |
interface vlan 23 |
|
Juniper JUNOS |
set interfaces ge-0/0/0 unit 0 family inet address 172.23.5.1/24 |
set interfaces ge-0/0/0 unit 0 family inet6 address 2001:db8:0:1::/64 |
How to generate an IPv6 Link-Local Address
A link-local address is always configured automatically for each link. It can also be configures statically if you like. This has nothing to do with a global address, like configure 1 step ahead. Link-Local addresses are mandatory, Global or other addresses on top are optional.
Watch my video here or read the text article below the video.
Rules
1. the block from which the address is assigned is always fe80::/10.
Please note: yes, this /10 block is large but the prefix for the generated Link-Local address is still always /64!
2. A Link-Local address has to be active for every interface on which IPv6 is enabled.
Link-Local addresses are needed for crucial network components such as Neighbor Discovery Protocol (NDP) and DHCPv6.
Steps to generate a Link-Local address:
- The host generates an address out of fe80::/10 using EUI-64 (see next chapter)
- The host performs Duplicate Address Detection (DAD) by sending an ICMPv6 Neighbor Solicitation message (NS) to the solicited-node multicast address belonging to the just generated Link-Local address
- if no ICMPv6 Neighbor Advertisement message (NA) is received, nobody else is apparently using the same address
- as long as Duplicate Address Detection (DAD) is not successful and still running, the new address is marked as tentative and is not yet used
- the new Link-Local address is usable
How Pv6 Duplicate Address Detection works
ICMPv6 Duplicate Address Detection (DAD) is used to make sure a (generated) address is unique .
It is used with Stateless Address Autoconfiguration, also known as SLAAC (see the following chapters) and Link-Local addresses (see the previous chapter)
How Duplicate Address Detection works
- Neighbor Solicitation (NS) message is sent to their own solicited-node multicast address, that was generated from the newly generated IPv6 address.
The source address is the unspecified address (::), as the uniqueness of new address is not proven yet
- Neighbor Advertisement (NA) message is received from another host, only in case the new address is already in use. This tells the DAD process that it failed and a duplicate address exists.
The target address for the Neighbor Advertisement message (NA) is the all nodes multicast group ff02::1, because the target does not use the new address yet, since Duplicate Address Detection was not (yet) successful.
- Usually – if no Neighbor Advertisement message is received because the address is indeed unique, it can be used and the DAD process ends successfully.
What is IPv6 EUI-64 Autoconfiguration
EUI-64 is the name of the method to generate the 64 bit interface Identifier , which is used for auto-generated addresses, such as a Link-Local address: fe80::xxxx:xxxx:xxxx:xxxx
In most implementations the 48 bit interface MAC address is used . Also unrelated numbers can be used for security reasons -> see IPv6 Privacy Extensions
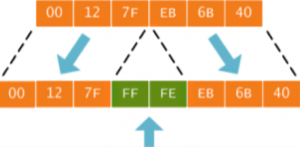
How EUI-64 is performed
The interface MAC address in this example is: 00:12:7F:EB:6B:40
A MAC address is only 48 bits, but we need 64 bits for the host identifier of an address with a /64 prefix. so to fill the remaining space:
EUI-64 Step 1
FFFE is placed in the middle:
EUI-64 Step 2
The Universal/Local (U/L) bit is switched to 1, because the MAC address is globally unique:
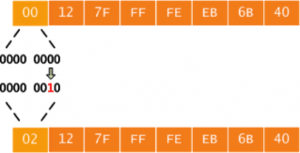
EUI-64 Result:
The new Link-Local address is: FE80::212:7FFF:FEEB:6B40
What are IPv6 Privacy Extensions
Regular Stateless Address Autoconfiguration (SLAAC) with EUI-64 uses the interface MAC address to generate a Link-Local address. It can also be used to generate a Global address out of the scope that a router on the locally connected LAN advertises via a ICMPv6 Router Advertisement (RA) message.
The host’s MAC address, or better: the network interface’s MAC address is theoretically globally unique. There are stories where multiple network interface cards shared the same burned-in mac address, but this is not common. It can happen especially in virtualized environments.
If you like to read more on the distribution of MAC addresses, you can use the free MAC address to vendor converter tool from Wireshark. The downside to this uniqueness is more the loss of privacy.
Security concern -> The host would be trackable around the globe using this unique bit of the IP address!
How you can make sure you are not tracked globally
Solution A: use a randomized interface identifier instead of the MAC address, as defined in RFC4941
- This approach is supported by some DHCPv6 implementations
- It has has privacy benefits, but it makes corporate client management more complex, such as troubleshooting, logging etc. because a client can have different addresses at the same time and these addresses can change constantly, so mapping a client to a user will be difficult.
Solution B: Stable Privacy Addresses as definied in RFC7217
- The generated address is not related to the client’s hardware MAC address, because it is not hardware based
- The address stays the same on the same network, so corporate client management is easier to accomplish
- The address changes as soon as the network is changed, for example by moving from the corporate network to a hotel WiFi network. The device is not trackable.
- This approach is usable for Link-Local, Unique Local (ULA) and Global address scopes
How to do Stateless Address Autoconfiguration (SLAAC)
Stateless Address Autoconfiguration (SLAAC) is used for automatic configuration of hosts on an IPv6 network. SLAAC uses the ICMPv6 Neighbor Discovery Protocol (NDP).
Watch my following video where I explain how SLAAC works with IPv6. Below the video I give you the written explanation.
How Stateless Address Autoconfiguration (SLAAC) is performed:
- First, a Link-Local address is generated using EUI-64
- The host sends a Router Solicitation message (RS) to the “all routers” multicast group (ff02::2)
- All routers on the local LAN reply with Router Advertisement messages (RA) and announce the prefix(es) that are used on the link
- The host generates an address in that prefix, with the host part (host identifier) again created using EUI-64 (or random numbers – see: Privacy Extensions)
- The host performs Duplicate Address Detection (DAD) to make sure the newly generated IPv6 address is indeed unique.
As long as the Duplicate Address Detection process (DAD) is not successful, the new address is marked as “tentative” and is not used - After DAD is successful, the address becomes active
The Transition to IPv6 – going Dual Stack
Now that you know so many things about IP in all versions, you might have one question – do I shut down IPv4 now, once I enable IPv6? How does the migration work?
Please watch my video or follow up with the article below.
Well, because not everybody is able to use IPv6 yet, and not everybody is still able to use IPv4 due to the shortage of addresses, we are aiming to run dual stack for all our network services.
Dual Stack operation means: using IPv6 side by side the current IPv4 implementation.
We should only use tunnels when absolutely necessary or for testing, but you should not use a non-native, tunneled IPv6 connection to provide your services to customers.
Dual Stack can be used as a transition path to IPv6-only. This may take a decade or so, before everybody is IPv6 enabled.
What does it mean to run IPv6 and IPv4 Dual Stack
Dual Stack provides full reachability for both address families:
IPv6-capable hosts are configured with IPv4 and IPv6
IPv4-only applications are only reachable via IPv4
IPv6-only applications are only reachable via IPv6
Which IP Version is used in a Dual Stack Environment for initiating a new Connection?
You are running Dual Stack in your network to gain critical insight into the new protocol and keep your network up to date. Great! You also know which IPv6 address is used by default for a newly originated connection. But in Dual Stack, which protocol – IPv4 or IPv6 is used?
When initiating a new connection in a Dual Stack scenario the source protocol is determined by the following rules, whichever rule matches first (tiebreaker):
- A Native IPv6 connection is used.
- A Native IPv4 connection is used.
- If there are no native connections, a NATted IPv4 connection is used.
- Finally, if nothing else is available, a tunneled IPv6 (6to4, …) connection is used.
IPv6 Source Address Selection
Having multiple addresses per host and interface is very common in IPv6! Have you been wondering which address is used as the source for initiating a new connection? There are simple rules that all operating systems have to follow:
Steps to determine the outgoing (source) IPv6 address, until a tiebreaker is found:
- Use the address from the same Scope or Type (Link-Local, Global).
- Use the smallest possible Scope.
- A preferred (non-deprecated) address is used.
- A transitional address (ISATAP, 6to4) is not used, if native IPv6 addresses are available.
- Prefer the Source-Destination pair with longest Prefix (/127 vs, /64).
- Prefer the address on the outgoing interface.
Recommended Resources for additional reading
Apart from the links throughout this course I recommend the following resources for additional information:
- The Internet Society (ISOC) IPv6 Portal
- Test your IPv6 connectivity on test-ipv6.com
- The official IANA list of assigned IPv6 address space is very interesting
- The Google IPv6 deployment statistics
- The RIPE NCC IPv6 working group and mailing list
Book recommendations on IPv6
I can recommend the following 3 books which I enjoyed reading:

This concludes IPv6 Foundation Part 5: IPv6 Configuration, EUI-64, SLAAC & Dual Stack of the original IPv6 Foundation Master Class.
Previous Part: IPv6 Foundation Part 4: ICMPv6 & IPv6 Neighborships
Next Part: IPv6 Foundation Part 6: IPv6 DHCP (DHCPv6)